Audit your network
in minutes, not days
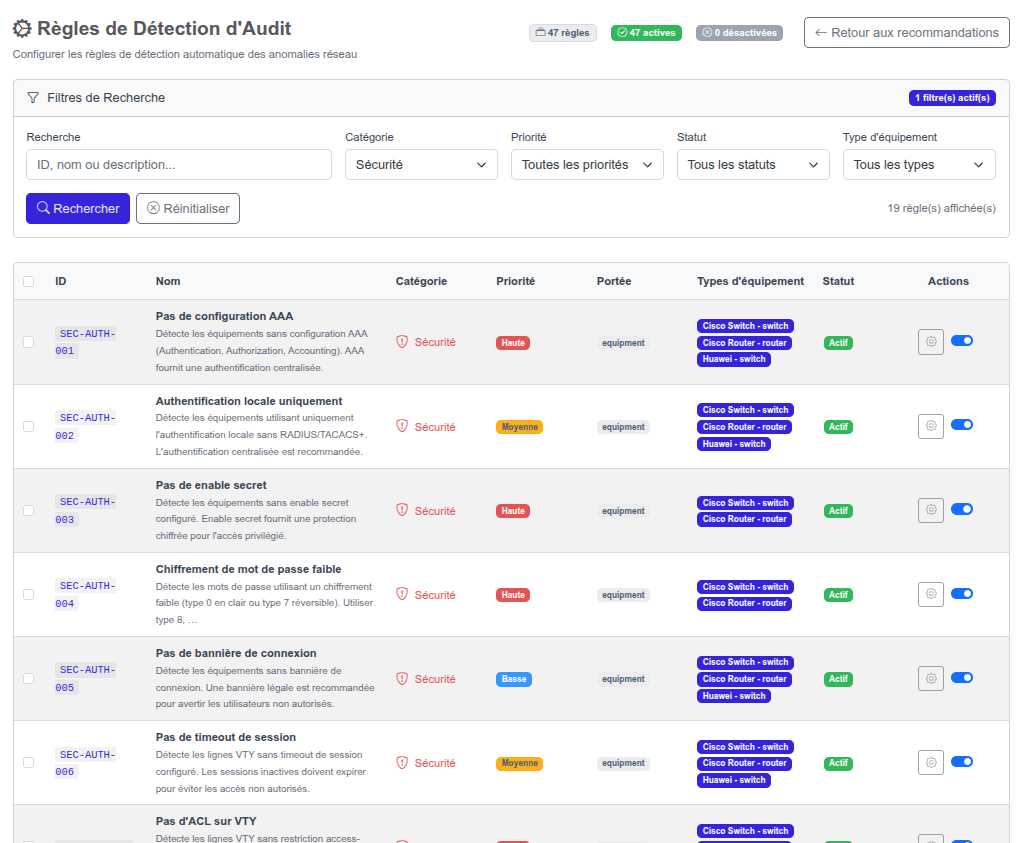
Automatic detection of configuration vulnerabilities across all your devices. A comprehensive catalog of customizable rules to identify risks before they become incidents.