Access your devices
without exposing credentials
SSH, RDP and Web from your browser, without VPN or shared passwords. Every session is recorded, every action is traced for complete auditing.
SSH, RDP and Web from your browser, without VPN or shared passwords. Every session is recorded, every action is traced for complete auditing.
Credentials hidden from users
Reviewable and auditable sessions
Browser access through probes
SSH, RDP and Web unified
In most organizations, network teams connect to devices with practices that expose the infrastructure to major risks.
Root and admin passwords are shared between technicians, stored in Excel files or shared notes. Impossible to know who uses which credential.
Heavy VPN infrastructure to maintain, unsuitable for external providers or one-time interventions. Each new team member requires a dedicated configuration.
Who connected to the Paris switch on Friday at 11 PM? What commands were executed? Without a bastion, these questions remain unanswered.
SSH/RDP ports open to the Internet, thick clients installed on workstations, disparate and uncontrolled tools. Every access point is a potential vector.
All connections to your devices go through the Intelligent Networks bastion. Credentials are stored server-side and injected automatically: your technicians connect without ever seeing a password.
Passwords are never revealed to users, not even administrators
The bastion injects credentials during connection, transparently
Change passwords at any time without impacting users
Combined with probes, reach remote devices from a simple browser
No more SSH clients, RDP software or VPN to access web interfaces. Intelligent Networks integrates all three protocols directly in the browser, with a native experience for each.
Interactive web terminal with escape sequence support, colors, copy/paste and full text recording
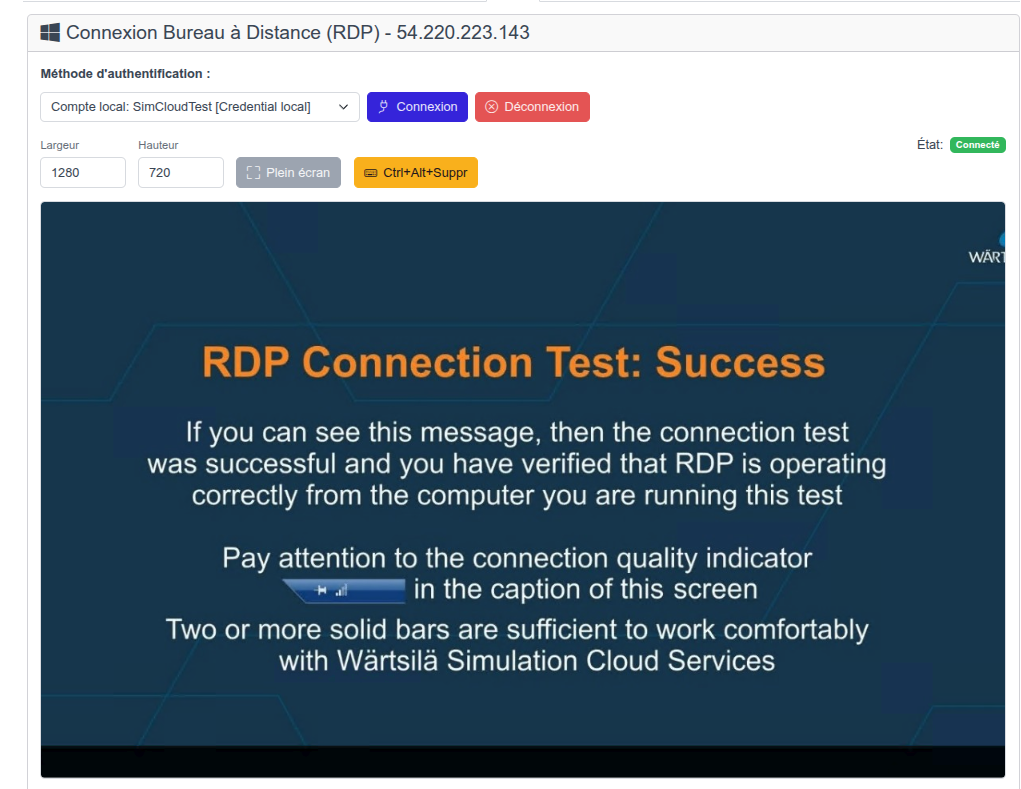
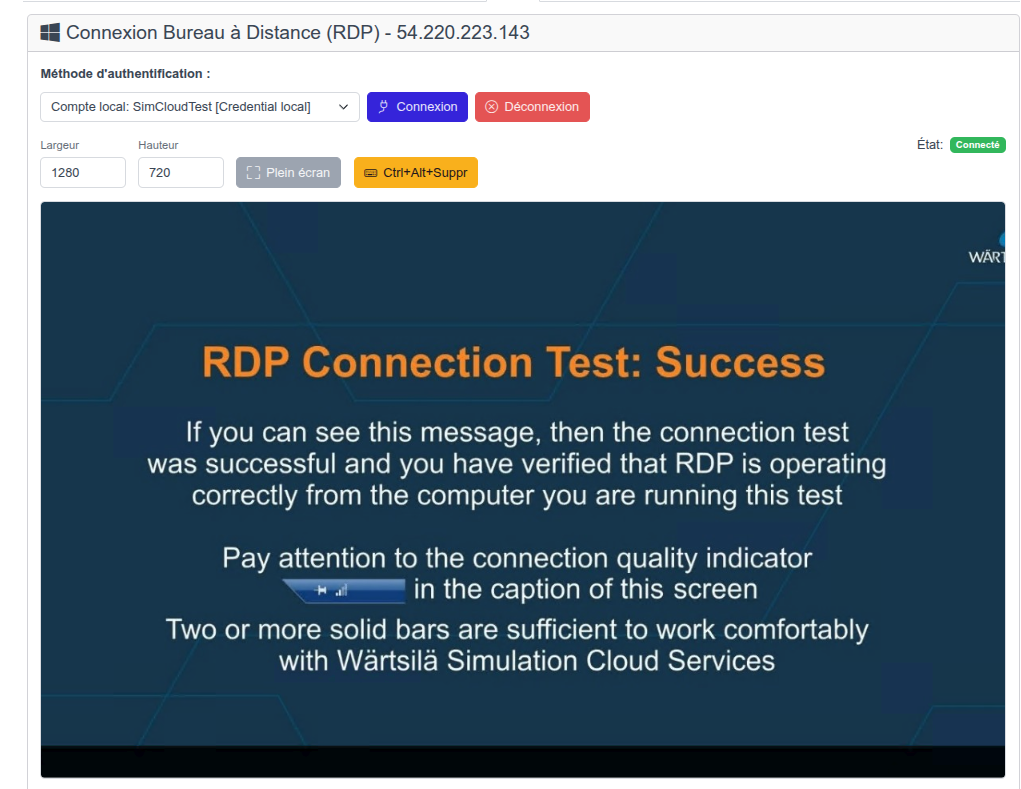
Automatic connection with stored credentials, dynamic resizing, clipboard transfer and video recording
Access management interfaces on non-routed networks, without publishing ports in DMZ, with centralized SSO authentication
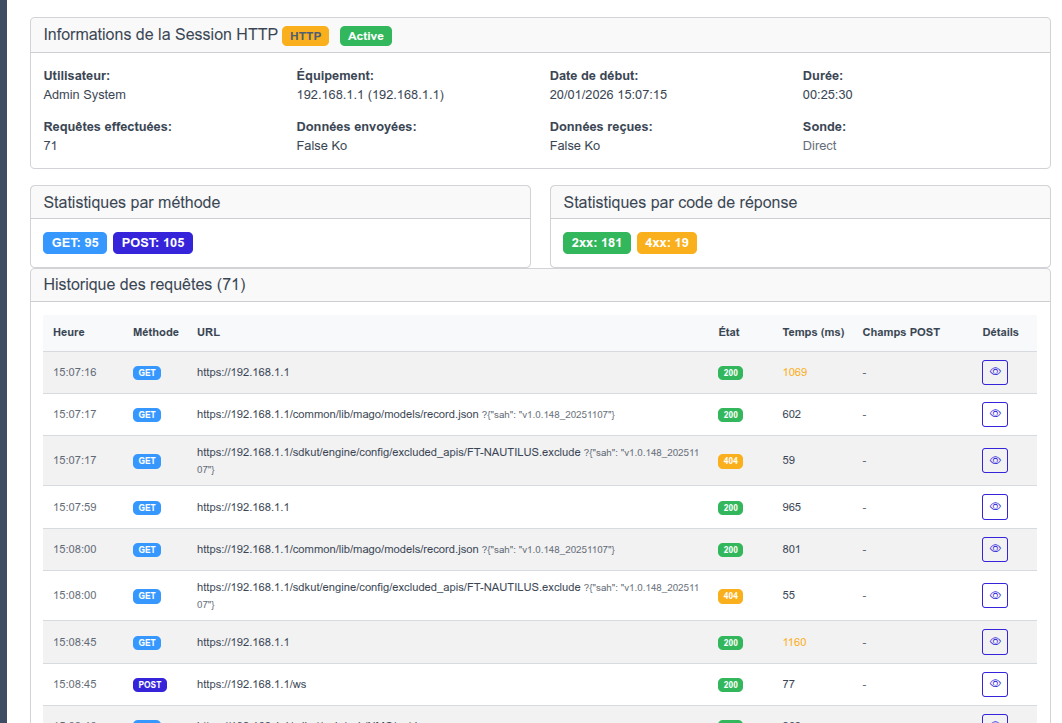
All sessions — SSH, RDP and Web — are automatically captured and reviewable after the fact. For compliance, investigation or simply knowing what was done on a device.
Full text recording (input/output), replay with display reconstruction and full-text search in commands
Full session video capture, timeline navigation, statistics by method and response code
Export recordings for long-term archiving or regulatory compliance
A flexible model combining roles (what a user can do) and scopes (where they can do it) for fine-grained access control isolation.
Define scopes by geographic site, company, device type or custom tags
Viewer (read-only), Operator (remote access), Admin (management) and Super Admin (all rights)
Each user receives a role applied to a specific scope for fine-grained and controlled permissions
Isolate access between companies, providers and clients within the same platform
How our bastion compares to market solutions
| Feature | Intelligent Networks | PAM Solutions | Open Source |
|---|---|---|---|
| Browser-based SSH | |||
| Browser-based RDP | |||
| Integrated Web proxy | |||
| Credential masking | |||
| Session recording | |||
| Granular RBAC | |||
| VPN-free access (probes) | |||
| Network inventory integration | |||
| Deployment complexity | Simple | Complex | Medium |
| Cost | Affordable | Expensive | Free |
The Intelligent Networks bastion adapts to all remote access scenarios.
Give temporary access to external providers without sharing passwords. Each session is recorded and revocable at any time.
Prove who accessed which device, when, and what actions were performed. Export recordings for your regulatory audits.
Connect to a remote device in a few clicks from any browser, without installing a client or configuring a VPN.
Change your device credentials at any time. Users don't know them: zero impact on their work.
Your technicians access network devices from home, via a simple browser, without VPN and without compromising security.
Centralize remote access across all your sites through probes. A single entry point for your entire infrastructure.
Integrated bastion, zero exposed passwords and complete session auditing